2 Sep
The highly popular poker improvement tool, PokerTracker, was recently the subject of a hack attack aimed at threatening users’ credit card details.
While users of the app PokerTracker 4 are thought to be unaffected, anyone running the software through either PokerTracker.com or the sub domain pt4.pokertracker.com will be contacted by Max Value Software, owners of PT4, by email in due course. In the meantime, they are advised to watch their accounts for any signs of suspicious activity.
However, most of the major credit-card providers only allow a 120-day window for people to appeal against any fraudulent activities which rules out these attacks which took place between December 23, 2018 through January 2, 2019.
Magecart
PT4 was, at that time, infected with a Magecart script whose aim is to rip customers’ payment information and is the same virus that was responsible for similar attacks on British Airways and Ticketmaster. It is believed that the offending Magecart code was specifically crafted for PT, who do not store billing information on their servers, to fetch and deliver sensitive data to the hackers.
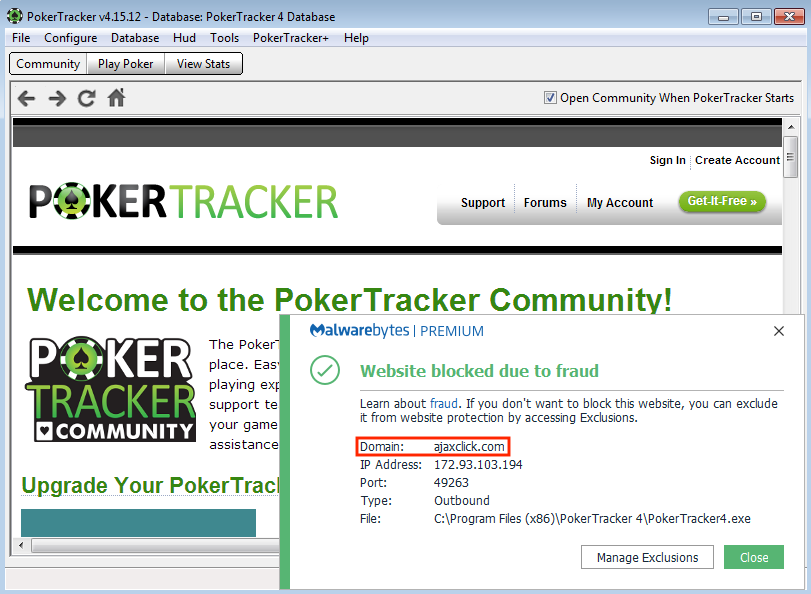
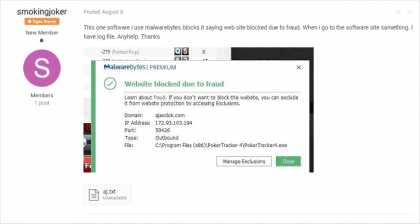
The attack only came to light as recently as August 8 after one user on the Malwarebytes forums, smokingjoker, reported suspicious activity on the poker software’s website. In his post, smokingjoker provides details that clearly show traffic being redirected from PokerTracker.com to an IP address which was home to ajaxclick.com.
Ajaxclick hosts numerous credit-card skimmers accredited to the notorious Magecart criminal ring and it’s from there that they managed to infiltrate the PT software and inject malicious code into pokertracker.com and its sub domains..
Outdated CMS
The attack was made possible because of Max Value Software’s, who also publish Hold’em Manager and Table Ninja, reliance on the outdated Drupal version 6.3x which was known to be highly vulnerable to these types of attacks. The latest release has been available since June.
Max Value Software and PokerTracker managing partner, Derek Charles believes the number of affected users to be in the low thousands and that, while usernames and passwords are safe, it’s recommended that users change their settings regardless. According to Charles, Drupal was removed within an hour of becoming aware of the incident some seven months after the infiltration.
